Keeping you in the know
Whatever you're interested in, get engrossed in our latest research, insights and blogs. We’ll put the kettle on, you have a browse.
Whatever you're interested in, get engrossed in our latest research, insights and blogs. We’ll put the kettle on, you have a browse.

30 min read
Our 2025 Email Security Trends report reveals insights from 400+ IT leaders and 2000 employees across the UK, USA, and Europe to uncover predictions, opinions, and insights into the state of email security.

20 min read
Learn how to prove the ROI of your solutions. Industry experts Simon Newman, Co-Founder of Cyber London, and Frank Horenburg, Head of IT at Zivver, share insights and expertise on identifying and sharing the value of security.

3 min read
7 min read
Everyone talks about data sovereignty - but why does nobody start with the low-hanging fruit?

9 min read
Every time an email containing sensitive data leaves your organization, is it safe to assume it is secure? The answer is, it depends. While you might know about TLS (Transport Layer Security) – the pr...
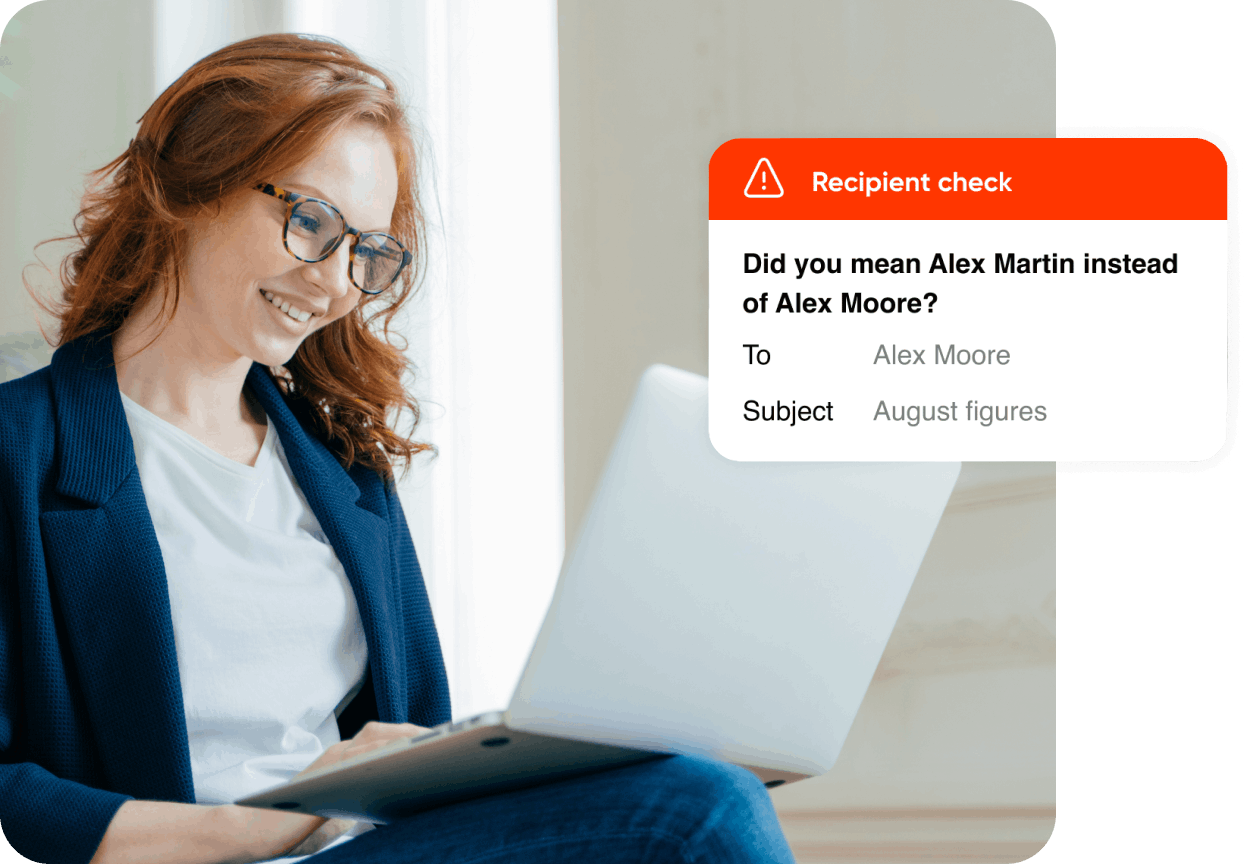
Learn how email data loss prevention keeps sensitive information safe.

30 min read
Our 2025 Email Security Trends report reveals insights from 400+ IT leaders and 2000 employees across the UK, USA, and Europe to uncover predictions, opinions, and insights into the state of email security.

Understand your encryption options for secure business comms
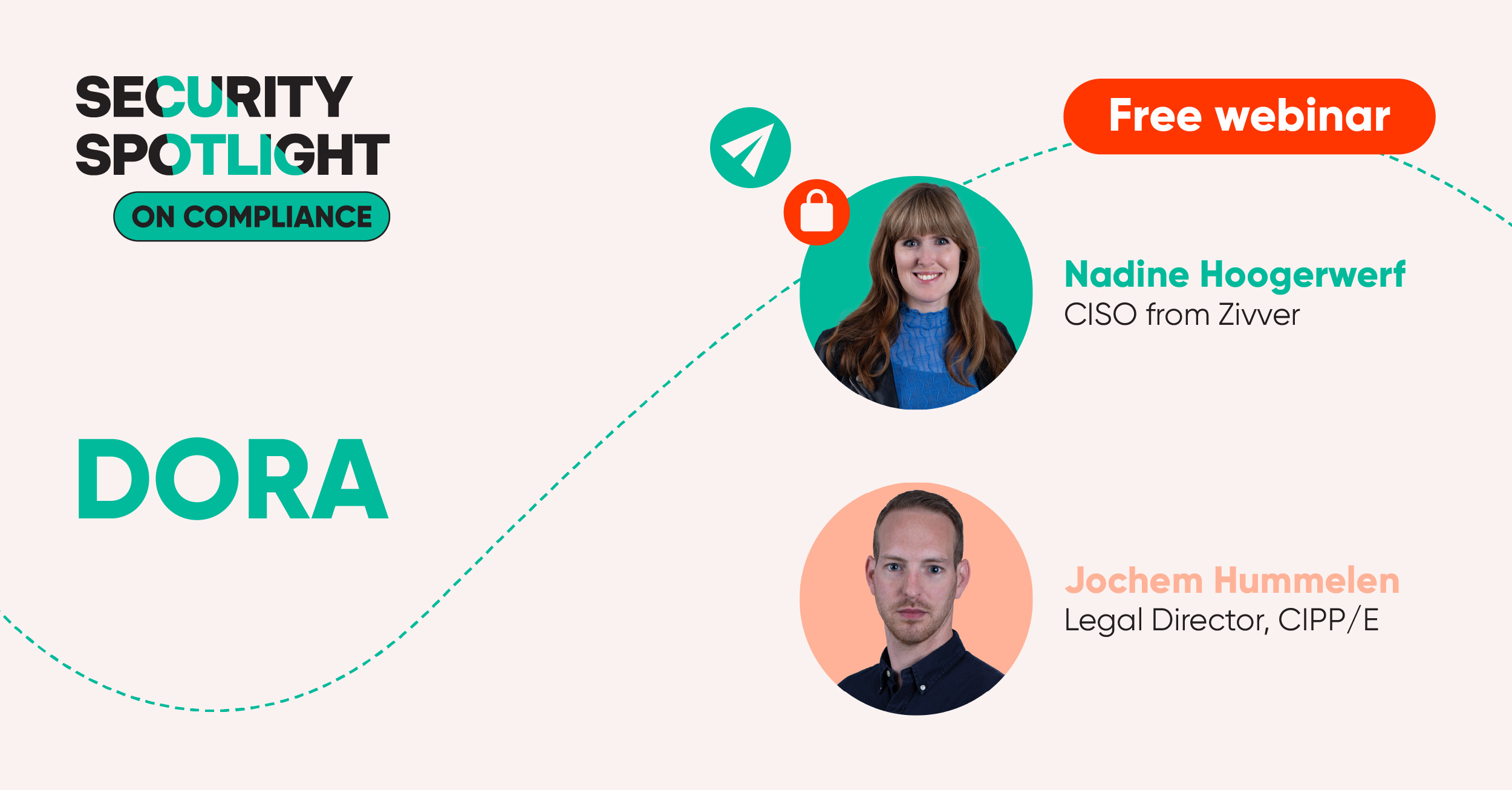
CISO, Nadine Hoogerwerf, and Legal Director CIPP/E, Jochem Hummelen, explore DORA, and share practical steps on how organizations can meet compliance.
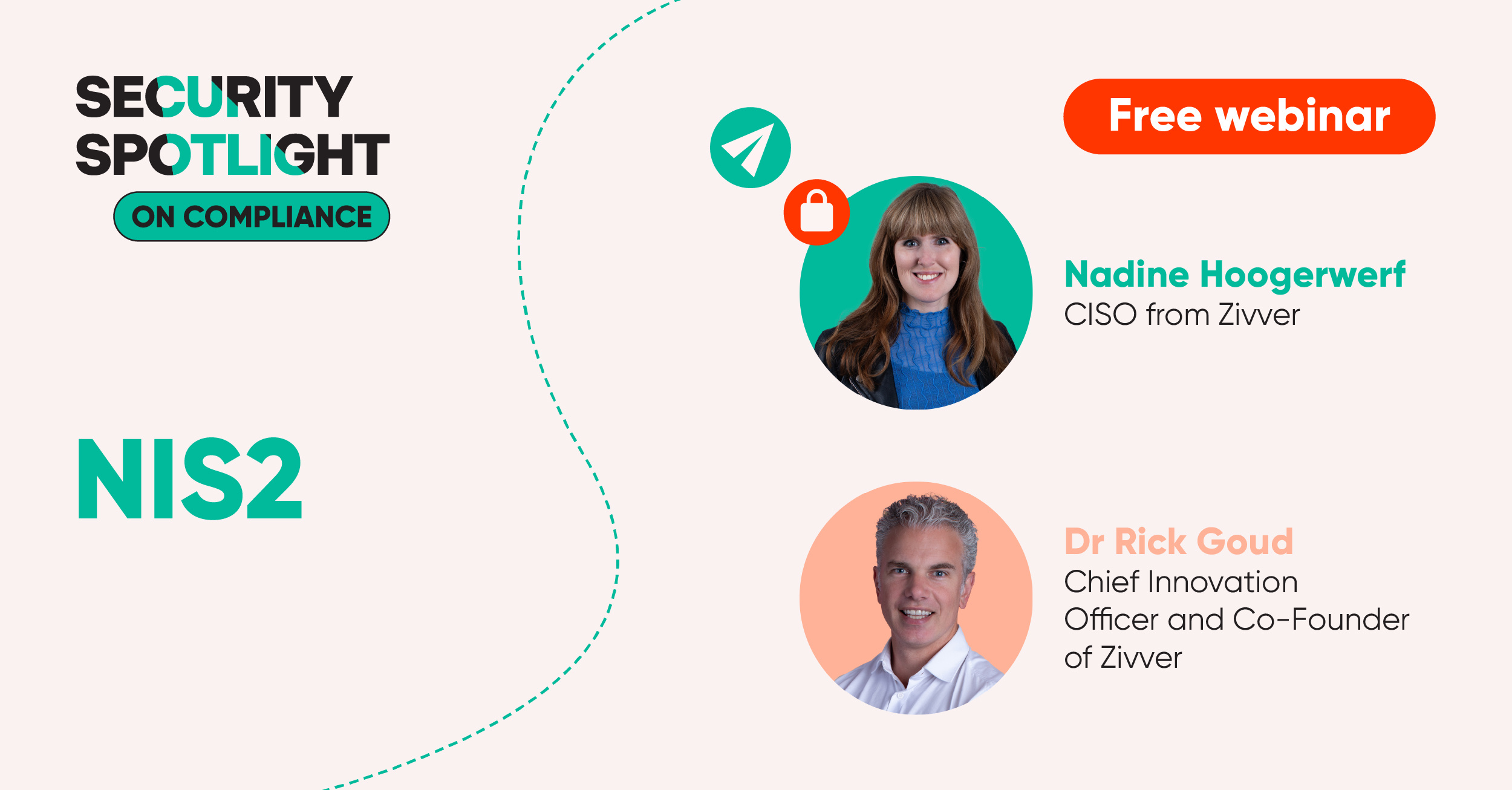
CISO, Nadine Hoogerwerf, and Chief Innovation Officer, Dr Rick Goud, explore NIS2, and share practical steps on how organizations can meet compliance.

59% of employees say they are worried that AI will make it harder for them to know if an incoming email or link is legitimate. So how can IT leaders protect people from phishing, malware and payloadless attacks?

4 min read
Combination delivers on commitment to uncompromising data privacy and security to European organizations Amsterdam, Netherlands – June 18, 2025 – Zivver, Europe’s leading provider of secure communicat...
2 min read
May 2025: Zivver is proud to announce its inclusion in the 2025 DataTech50 list by FinTech Global, recognising the company as one of the most innovative technology providers driving transformation in ...
2 min read
Zivver founders Dr. Rick Goud and Wouter Klinkhamer celebrate 10 years since launch of Zivver
Subscribe to get more email security tips straight to your inbox.